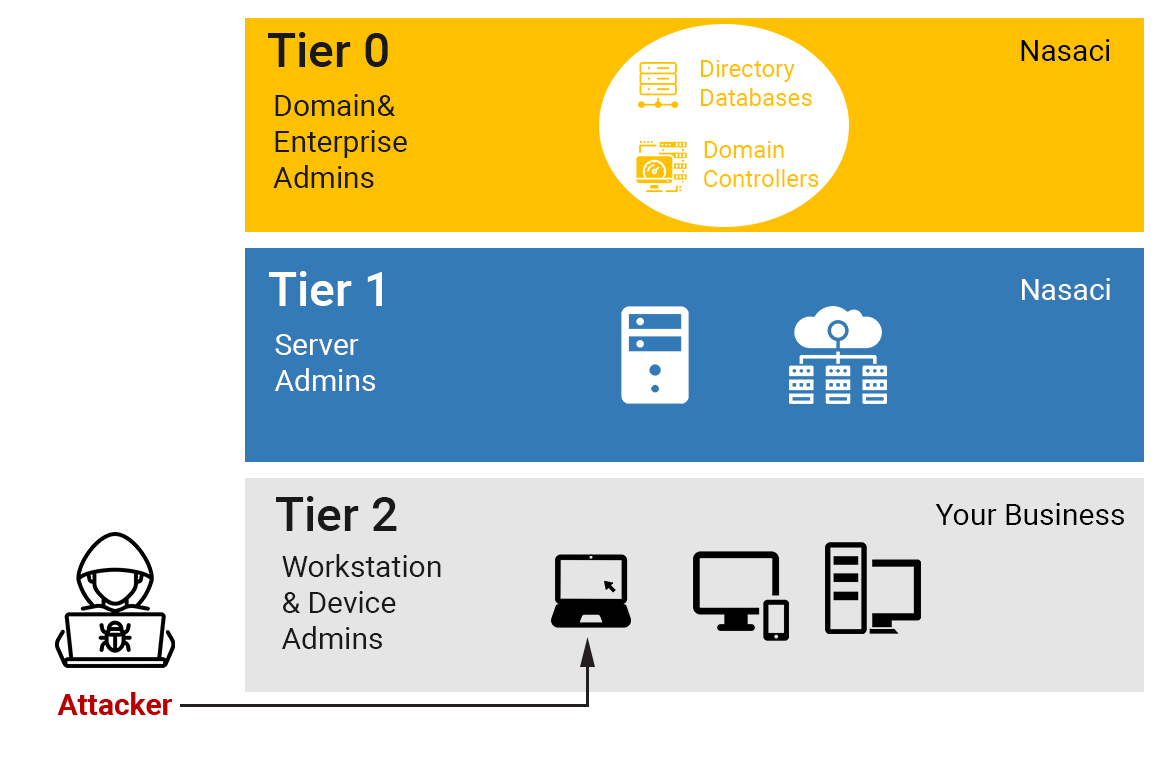
Phishing Attacks, etc
Lateral Movement
a. Steal Credentials
b. Compromise more hosts and credentials.
Privilege Escalation
a. Get your Domain Admin Credentials
Execute Attacker Mission
a. Steal data destroy systems
b. Persist Presence
NASACI provides different types of cyber-security through technology partner Companies Security Intelligence Platform unifies SIEM, log management, file integrity monitoring, network forensics, host forensics and compliance automation to help reduce the time to detect and respond to cyber threats. We can help clients across the world tackle their security and compliance issues. NASACI provides our customers with sensitive data information additional biometrics cyber security products within the health and financial services.
In addition, NASACI virtual machines, your VMs, virtual servers are totally SHIELDED, only you as an owner are able to access your information. You have logical system administration, no need for human intervention, no risk for your private information to be access by administrators and operators unless you authorized and for a measured limit of time only by knowing the person to whom you are granting limited time access and if needed.
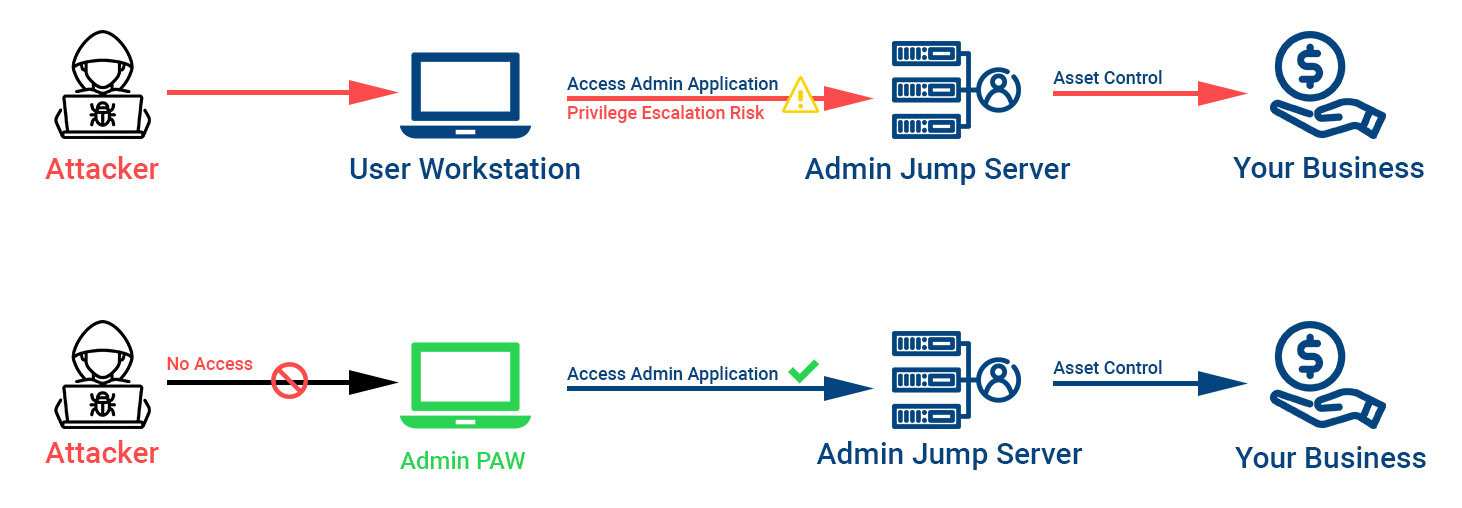
NASACI Engineering understand that an everyday computer with unrestricted Internet access, email, and LOB, (your business) applications is much more likely to be compromised because often your laptops, computers, cash registers, or other systems have not had (or cannot have) many of the latest protections applied to them to prevent compromise and attaches against your business.
NASACI follows strict guide lines from Microsoft protecting our data center, our work stations, our customers computers and business tools by constantly patching our and your applications layer aggressively making sure the servers and Operating systems are always within the 30 days or even weekly of the patch’s release, NASACI runs the latest version of Windows turning on the latest protection features that can help to stop known and unknow malware.
Antivirus, etc. do not properly help; NASACI protect and isolate all administrator’s credentials by using dedicated Privileged Access Workstations (PAWs) to work with your business systems and applications.
There is not 100% cybersecurity protection; NASACI works with the best practices and recommendations to protect your business.